Wsus Script Force Update Detection Limit Definition
Wsus Script Force Update Detection Limit Calculation. Install this update to revise the definition files that are used to detect viruses, spyware,. Restart-Computer -Force. This update might force me to uninstall Windows 10 if this is the level of respect Microsoft is now showing towards it's users. That's interesting.
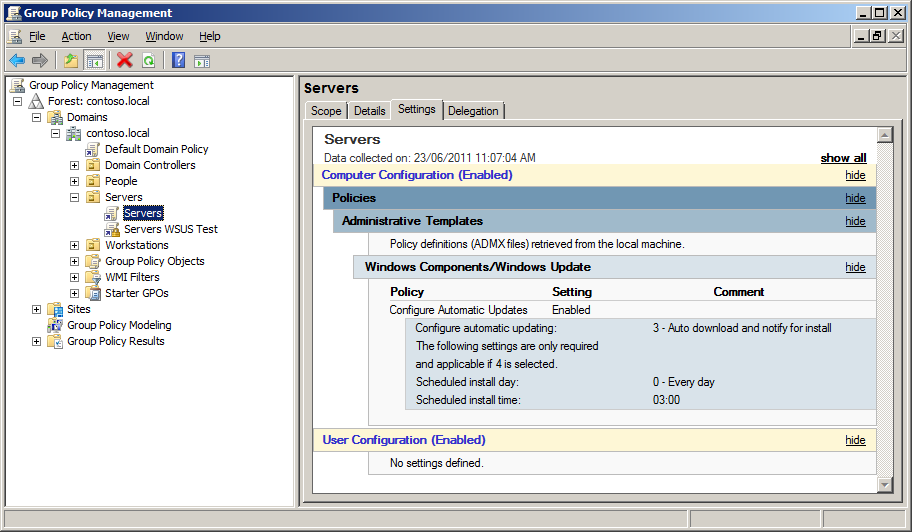
If you google the issue, it appears that Windows 1607 doesn't play nice with WSUS. It likes to get stuck downloading updates and never go anywhere. I've tried setting the GPO option here to bypass with the intent of making sure the box gets updates straight from WSUS and not from other clients. Adding KB3176495 as a preinstall package for one of my deployments via MDT seemed to help but it isn't working now. Also adding KB3176929 made no difference (both of these are referenced by multiple threads) Get-WindowsUpdateLog is of no help since I guess it needs some symbols to make the data readable.
Cara Mengganti Lagu Di Guitar Hero PS2. Pake untuk mengganti lagu standar di GH2 ini beserta file' chartnya yang sudah kita bikin dengan menggunakan software FeedBack Chart, yang kemudian kita konfer menjadi file MID. Caranya mengkonfer/merubah file chart menjadi file MID adalah sebagai berikut. Cara merubah temp chart guitar heto di feedback.
WSUS server has both of the Windows 10 related updates (including the one that required additional steps after installation).esd and now.msu are registered in MIME types. Windows 1511 updates no problem and you can even start the 1607 update from WSUS if I approve it for a computer. Just for once, I wish that one of these 6mth updates could go off without some sort of major hitch! Hi everyone, and apologies for the frustration you're experiencing. This thread calls out several different symptoms, for each of which I'll provide guidance.

Note that Configuration Manager will exhibit the same symptoms as each of the scenarios below. WSUS 3.0 SP2 on WS08R2 SP1 (or unpatched WS12/R2) cannot download ESDs This is by design. WSUS 3.2 cannot sync or distribute ESDs, and WS12/R2 can only do so if both KB3095113 and KB3159706 are installed on the machine, and all necessary post-install steps from KB3159706 have been followed. As folks have noted, these post-install steps [and the general way that this update was released] caused unnecessary pain and confusion.
We'll choose a less disruptive strategy for future WSUS updates. Clients have upgraded to 1706 using Anniversary Update, but cannot get Cumulative Updates This is a bug in the Windows client that will be fixed in an upcoming cumulative update. In the meantime, clients may experience some delay in getting the monthly content, but they will eventually download it. The workaround here is to simply wait longer than usual, or to scan directly against Windows Update if you've waited several days and haven't seen any download success in that time. WSUS can sync/distribute feature updates (such as 1511), but cannot deploy the 1607 feature update This is a newly reported issue that we are currently investigating.
Again, the workaround is to pull the 1607 feature update from Windows Update instead of WSUS. We understand why you might not want to pull such a large file from the Internet once for each of your clients, and are figuring this out as soon as we can.
Penilaian kinerja wakil kepala sekolah. We'll share further updates on the investigation as they become available. Regarding SmartDrv's post, and the thread linked mentions it, I got it to work on my WSUS server by adding the.esd MIME type to IIS. I'd done all the other stuff previously. I think all I did after that was restart the WSUS Service and I was able to update my 1511 machines to 1607. Only annoying bit about this has ben having to upgrade the VM that is my main WSUS server to be compatible with Workstation 12 from 11.something so I could setup a larger disk for the update files. (Granted I run/test a lot of MS OS's and apps, but 600GB wasn't enough.) Once I move it to vSphere I'll be able to give it more space.
And the ADMX is slightly different, so our security folks will have to review it again. You have to have security reviews of an ADMX file?
It doesn't even do anything on its own. Not the file itself, but the settings. They're (to our eternal frustration) trying be as close to the STIG recommendations as possible, and asked us to setup GPOs based on that for testing. Problem #1 is whoever is making those STIG recommendations has never, ever tried to use a PC bound by those settings, because it leaves machines unusable. Problem #2 is that because of Problem #1, nobody can test anything with the recommended policies in effect. Problem #3 is they expect us to figure out which of about a thousand settings is causing things to fail. Problem #4 is if you apply all the GPO's to a Windows 10 machine, for some unknown reason they can't be removed, replaced, or updated even if you leave the domain altogether.